For service providers
Protect your network from illegal robocalls and regulatory risk
Illegal robocalls and bad-actor traffic from customers or partners can trigger major FCC or state fines, waste valuable network resources, damage your reputation, and limit safe revenue growth. Our services help you achieve compliance faster, dramatically reduce mitigation effort, and grow revenue safely. Watch exposes risky customers and partners with evidence-based insights that cut investigation time and cost. Score blocks problematic calls at the network level before they consume resources or generate complaints.
Get Started Today
Watch
Root out risky robocallers
Pinpoints sources of illegal activity with rich, actionable evidence
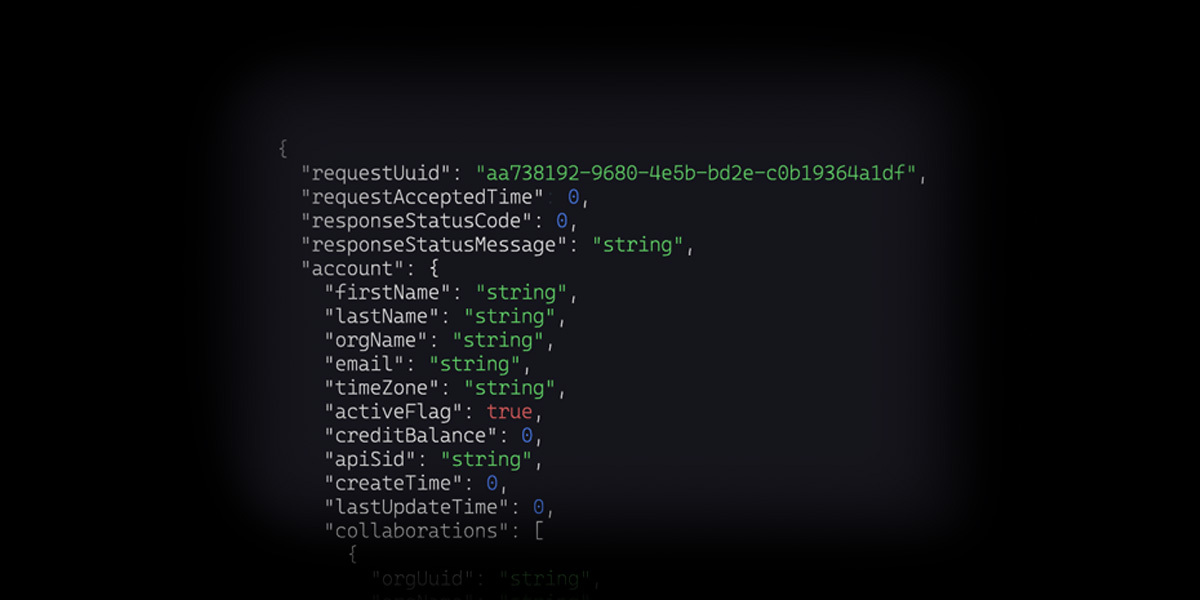
Delivers dashboards, reports, and APIs that fit your existing workflows
Cuts investigative time and costs with defensible intelligence
Score
Block risky robocalls
Delivers real-time phone number risk scoring with transparent rationale
Provides easy-to-integrate APIs for fast, seamless deployment across your network
Stops known bad traffic from consuming resources, triggering complaints, or creating regulatory exposure
Want to get started for free?
Join our Fastlanes program
Fastlanes is designed to eliminate imposter fraud involving our enterprise clients by rapidly taking down or restricting reach of numbers involved in fraud. It takes only minutes to sign up to be notified when you are the source of or carrying that fraud, so you can take action.
Learn MoreRapid, measurable ROI
Bad-actor traffic creates rising regulatory exposure, wasted network capacity, and missed revenue opportunities. Our service detect and support addressing problematic behavior early, delivering clear business impact. Clients report up to 90% reductions in fraudulent traffic, 15%+ reductions in network and compliance costs, and stronger safe revenue growth — with many achieving full payback within the first 3–6 months through lower mitigation effort, improved efficiency, and increased revenue.
Reduce regulatory risk
Stop risky traffic at the source to dramatically cut traceback requests, legal exposure, and potential FCC or state fines, often reducing compliance-related costs by 50% or more.
Safely grow revenue
Identify bad behavior quickly so you can confidently accept more new customers and origination traffic while minimizing risk and staying in compliance.
Lower operational costs
Eliminate the expense and complexity of building and using homegrown monitoring tools while reclaiming valuable network capacity previously consumed by bad traffic, delivering immediate and ongoing savings.
Boost answer rates
Leverage actionable intelligence to remediate spoofing and unlawful behavior faster, resulting in higher answer rates and better completion for your legitimate traffic.
Want to understand your network's ROI?
Request demoFrequently asked questions
Can your services help with robocall mitigation plans?
Can your services help with Know Your Customer (KYC) efforts?
What does your pricing look like for service providers?
How do you compare to alternative services?
Ready to protect your network from telecom troublemakers?
Contact us for a tailored demo to learn how YouMail Protective Services can help your service provider business stay compliant and profitable, using our exclusive insights, proven approach, and support for rapid mitigation.
Request Demo